An introduction to DLT concepts and why I think IOTAs Tangle is superior to Blockchains

Disclaimer: Nothing in this article should be considered as investment advice.
The goal of this article is to help newcomers in the cryptocurrency space or anyone unfamiliar with the technology behind it to understand what Distributed Ledger Technologies (DLTs) are and why we need them. Therefore, I will try not to go too deep into the technical details of DLTs, but rather give an overview of the principles used. I know this is a long article, but I wanted to explain everything in one document so you don’t have to look in different places if you want to get a basic understanding. Feel free to skip parts you already know. It’s important to note, that I won’t discuss all possible attack vectors or every detail of the tech. This article should only be an introduction to the topic and the first stepping stone to dig deeper if it sparks your interest.
I’m going to talk mostly about cryptocurrencies because this is an easy example to understand, but there are a lot of other exciting use cases for DLTs (maybe I’ll talk more about them in a future blog post).
The Blockchain and Tangle sections have a short TLDR paragraph in the beginning explaining what they are. If you read the whole article, you can skip these TLDR sections as everything will be explained in more detail afterwards. If you have questions about this blog post, feel free to ask in the comments. So let’s dive into the topic.
To understand why cryptocurrencies were created in the first place, let’s take a quick look at how currencies have evolved in the past and how the current system works.
What is Money and why do we use it?
Before the concept of money was created, people already exchanged goods by bartering. In the right circumstances, bartering can be very simple and effective. Lets say Alice wants to trade some apples for a pair of shoes. If she can find someone that wants to trade shoes for apples, this system works perfectly. A challenge arises when Alice wants shoes from Bob, but Bob doesn’t like apples and asks for some bread instead. In this case, Alice must first find someone who wants to trade bread for apples, and then exchange that bread for shoes. This can get very complex and requires a lot of coordination between different people. So bartering can be simple and direct, but getting what you want in exchange for what you have may require coordination between more than just you and the person who has what you want.
A solution to this problem is a common medium of exchange that allows everyone to trade directly with each other. Money is this common medium of exchange. Early forms of money possessed value regardless of their currency status (currency is money in circulation), such as bushels of barley. This ensured confidence in the currency, as anyone could make use of it and it was therefore unlikely to lose value. Another advantage with bushels of barley is that bushels of the same size are not easily distinguished from each other and therefore have the same value. However, this form of money also had some obvious disadvantages, as the bushels were inconvenient to carry around and also degraded if not used or quickly traded away.
To solve these drawbacks, new money in the form of precious metals, especially gold, evolved. This new form of money was very convenient to carry around (at least the amount required for daily use) and did not deteriorate over time. Compared to bushels of barley, however, it required much more trust, because gold had less underlying value, apart from its use as currency or jewelry. Since it was impractical to divide gold into very small amounts for purchases like a loaf of bread, banks emerged that offered to store the gold for you in exchange for promissory notes. These promissory notes now could be used to make purchases or taken to the bank to be exchanged back into gold. This was the birth of paper money.
Since the abolition of the gold standard, currencies today are no longer backed by anything physical, but by the promise of the states to keep the monetary system running. This centralized the power over the monetary system into the hands of the currency-issuing entities (the central banks). Therefore, everyone using these currencies must trust the central banks, because theoretically they could create as much money out of thin air as they want, thereby devaluing the savings of everyone who uses the currency. Another thing that changed is that nowadays most transactions are done online rather than in person.
How do these online transactions work?
Suppose you want to exchange some money with Bob without meeting him in person and handing it over in cash. Currently, you probably use a bank transfer or other companies like Paypal for this. In principle, these third parties all work in the same way: They have a large central database where they store their user data such as names and account balances. If you want to send 20 $ to Bob, you send this request to the third party and they subtract 20$ from your balance and add 20$ to Bob’s balance in the database.

This whole process works very well as long as the central database is protected and the company is honest and doesn’t make mistakes. However, if just one of these three requirements is not met, your money is at risk. If a hacker somehow gains access to this database, he could manipulate it at will, e.g. add a few zeros to his balance or set your balance to zero. The same applies to all employees of the company who have access to the database. So, you have to trust the third party that everything will be handled correctly, and in addition, you have to pay a fee for their service.
If you want to eliminate the need for trusted third parties (in this example Banks or Paypal), you need to find a decentralized way to secure and update a database that stores all relevant information. DLTs can provide you exactly this functionality, as they shift the requirement for trust from companies to mathematics and algorithms.
The problem DLTs want to solve
To be able to understand why a particular technology is better than the other, one must first understand the problem they want to solve. The goal of any Distributed Ledger Technology (DLT) is to process, store and share data in a trusted manner without the need for intermediaries. This data can be anything, but to illustrate the principles used in Blockchain and the Tangle, we will focus on currencies as an example use case in this blog post.
What is a Blockchain and how does it solve the problem?
TLDR:
A Blockchain is quite literally what the name implies: a chain of blocks. Each block consists of a list of transactions. The blocks are chained together using a cryptographic hash function that ensures that the transactions cannot be altered. This Blockchain is then shared openly so that anyone can download a copy. To include new transactions and update the Blockchain, a temporary leader is selected by the network and is allowed to create a new block. This leader role should change to different people as often as possible to make sure you don’t have to trust any one of them.
What do we need to build a cryptocurrency?
To better understand the principles used and why they are necessary, we will go through how we could have invented our own cryptocurrency using a Blockchain. To be usable as a currency, our system should be able to:
☐ securely store all required data
☐ send and receive transactions
☐ ensure that all transactions are valid
☐ ensure that everyone in the network agrees on the ledger state (who has what balance), i.e., reach consensus
If we succeed in designing such a system, we will have achieved our goal of creating a system capable of processing, storing, and exchanging data in a trustworthy manner, without the need for intermediaries.
The first question we will answer is how to securely store all required data using a Blockchain.
What is a Blockchain?
A Blockchain is quite literally what the name implies: a chain of blocks. Each block consists of a list of statements. These statements could be anything, but in our example, they will be transactions in the form of “Alice pays Bob 20¢”. So a single block looks something like this:

After a predefined period of time, a new block is created and all new transactions are written into this new block. In addition to the transactions, a hash pointer (will be explained in a second) to the previous block and a nonce (more on this later) are written into this new block.
The image below shows what a Blockchain looks like. Note that I use names instead of public keys (explained later) to make it easier to read. The transactions in real Blockchains look different, but the principle remains the same. Don’t worry if you don’t understand everything in the picture yet, I will explain every part of it.

The Blockchain will play the role of the central database of companies, storing the transactions of each user.
What is a hash pointer?
A pointer is simply an arrow directing us somewhere (in this case to the previous block). The result of a hash function is called a hash. Hash functions have the following properties:
- same input always leads to same output
- can take an input of arbitrary length and produce a fixed length output
- small changes in the input will lead to large changes in the output
- you can’t use the output of the function to calculate the input
- the probability that different inputs lead to the same output is very very small
The image below shows that hash functions can be used to check whether the content of a file has been changed after it was created. I’ve used SHA256 (Secure Hash Algorithm) as an example and you can use online converters like this one to check it yourself:
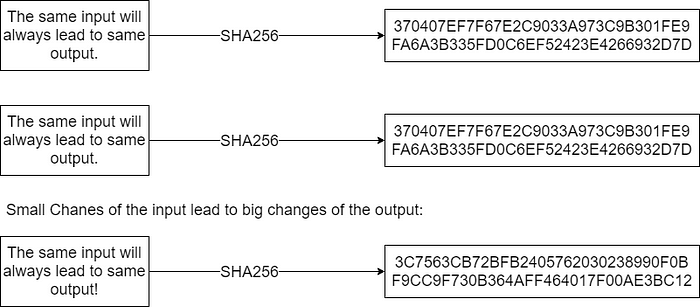
So the hash pointer is basically a data structure that allows us to know where the previous block is stored and whether its content has changed since it was created. As the blocks are chained together using the hash pointers, the resulting data structure is called Blockchain. The Blockchain will play the role of the central database of companies, storing the transactions of each user. So now we have a way to store the relevant data and make sure, that no one can change the content of a block after its creation without everyone noticing.
But there are still a lot of open questions that need to be answered before we can use a Blockchain-based currency. The first one is:
Isn’t the Blockchain a single point of failure, just like the central database of banks?
A key difference to a central database is that the Blockchain is decentralized (shared publicly), so anyone can download a copy and verify that all transactions are valid (more on that later). Computers that download and validate the Blockchain are called “nodes”. Decentralization eliminates the problem of the database being a single point of failure in the system. If the Blockchain on one computer is corrupted, it doesn’t mean anyone’s funds are at risk. It just means that this copy of the Blockchain is recognized as invalid by all nodes (because the hash of the hash pointer will have a different value) and is therefore discarded. You can download a new copy of the valid Blockchain to fix this problem.
Now our system is able to:
☑ securely store all required data
How do we send and receive money?
To participate in the network, each user needs a private and a public key. The private key is basically a very long number and you can think of it as the password to your funds. You need your private key to sign outgoing transactions so whoever has access to your private key has control over your funds. It is very important that you generate your private key securely with some form of random number generator (DO NOT use an online generator for this!) and never share it with anyone (who should not be able to transfer your funds). You should also make sure that you keep this private key safe, because if you lose it, all your funds are lost as well. The private key is the single most important piece of information for a user of the network and cannot be reset like a password. I can’t stress this enough: Take good care of your private key and don’t share it with anyone!
Now you may wonder, if your private key is only a number generated by a random number generator and that important, what would happen if someone randomly generated the same private key. If that would actually happen, this person would have full access to all your funds. However, the number of your private key is so long that the chance of this happening is infinitely small. 3Blue1Brown made an excellent video that tries to illustrate how small this chance is. So as long as you choose a truly random number as your private key, you can be very confident that no one will generate the same private key.
The private key is used as input for a cryptographic function (e.g. a hash function) that generates your public key. You can think of your public key as an account number. You can share this information with others so they know where to send the money when they want initiate a transaction to you. If you lose your public key, you can recover it using your private key, but it is impossible to calculate your private key with your public key.
In summary, the private key is required to send transactions. You use it to sign them to make sure that it’s really you sending the funds. Other users of the network can verify the validity of your signature without you having to reveal your private key (I won’t go into the technical details of how this works in this article). Your public key is required to receive transactions, as it’s used to generate your wallet address.
You may have heard that Blockchains are anonymous. In fact, most of them are just pseudonymous because anyone can see anyone’s public keys. If someone is able to link a public key to a specific person, they can track all your purchases. To protect your privacy, you can use a new public key for each transaction.
Now we have found a way to:
☑ send and receive transactions
How do we make sure that all transactions are valid/honest?
With the Blockchain, we have introduced a way that can securely store transactions and prevent tampering after they are created. But how do we make sure that transactions are valid at the time they are created, i.e. when they are written in the block?
A transaction is valid if:
- input amount = output amount
- input tokens (coins) aren’t already spent somewhere else
- issuer of transaction signed it using his private key
Let’s look at a few examples:

The second transaction is invalid because Alice didn’t sign it. The third transaction is invalid because Bob didn’t sign it. The fourth transaction is invalid because Alice doesn’t have enough funds after the first transaction. The fifth transaction is valid because Bob signed it and he also received 200¢ from Alice in the first transaction, so he has enough funds.
A block is valid if:
- all transactions in this block are valid
- contains the correct hash pointer to the previous block
- contains correct block reward (more on that later)
- in Proof of Work (POW) systems: contains nonce with correct difficulty (more on that later)
All nodes in the network check each new block for validity. If they detect an invalid block, they reject it. This ensures that only valid blocks (and thus valid transactions) can be added to the Blockchain.
This system allows us to:
☑ make sure that all transactions are valid
How do you decide who gets to create a new block?
In a distributed system like ours, where multiple nodes store the same data, we need a way to decide who gets to update the Blockchain. Otherwise, each node would update its own Blockchain in potentially different ways, resulting in a lot of different Blockchains. So, we need to find a way to ensure that all nodes update their copy of our Blockchain in the same way to reach consensus on the data. Blockchains do this by selecting a single leader who gets to create the new block and decide on its content. If the new block is valid, all nodes accept it and append it to their local copy of the Blockchain, ensuring that all copies of the Blockchain look the same. But how do we choose the leader?
To keep our network decentralized, we need to make sure that the selection of our leader is not always the same person (or, more precisely, a node of that person). Otherwise, we have to trust that person and our Blockchain wouldn’t have any advantage over the banking system. So the more decentralized our system is, i.e. the more different people are chosen as leader, the better, as each leader has less power over the network if the leader role changes very often.
The most intuitive idea might be to just randomly select a node of the network and let it create the new block. However, this idea has some problems. Since hosting a node is very cheap, a user of the network could create hundreds or thousands of nodes to increase the probability of being selected for the block creation without using a lot of resources. This process is called sybil attack and would lead to a centralization of our system and we just discussed why this is bad. We also can’t make node creation expensive to solve this problem, because that would lead to fewer people running nodes and thus centralizing our system. So we have to find a more complex way for our leader selection.
Since virtually all current Blockchains use either Proof of Work (POW) or Proof of Stake (POS) for their leader selection, I will briefly explain both concepts:
Proof of Work
As the name suggests, you’ll have to do some work to be eligible as a leader. This work consists in trying a cryptographic puzzle over and over again until you get lucky and solve it. The computers that try to solve this puzzle are called “miners”. The first miner that solves a puzzle is chosen as leader and gets to publish a new block on the network. If this block is valid, all nodes will append it to their copy of the Blockchain and the miners will start solving a new puzzle for the next block.
Since we have already talked about hash functions and their properties, we can now go into more detail about how this puzzle works. Miners add the transactions they want to include to the new block and then calculate the hash of that block. To be valid, this hash has to start with a predefined number of zeros, which is called the difficulty. Since you can’t use the output of the hash function to calculate the necessary input, and a small change of the input leads to a large changes in the output, you have no other way to solve this puzzle than to simply try different inputs and hope for the best. To be able to vary the input of the hash function without changing the transactions, you include a nonce into the block. This nonce is just a number, and you try to find the correct value for this number so that the hash of the block starts with the right amount of zeros. You can calculate the chance of hitting a hash with difficulty 30 (hash has to start with 30 zeros) using:

So you need about 1 billion tries to find the correct nonce at this difficulty. If you increase the difficulty, you will need more tries to find a valid block. This means that the difficulty can also be used to set the average time between new blocks. If the hash rate (number of hashes that can be calculated per second) of the network increases because new miners join the network, you can increase the difficulty so that the time between blocks stays the same, and if miners leave the network, you can decrease the difficulty.
Now we learned that the work in POW systems is to find the correct nonce. Since you publish this nonce with the block, all nodes can easily validate that you actually did the work without doing the same amount of work themselves by calculating the hash of the block and checking if it starts with enough zeros.
The chance that you will be selected as a leader is equal to the proportion of your hash rate compared to the hash rate of the entire network. The more computing power you use to solve puzzles, the higher the chance of being selected. However, increasing your computing power is very expensive because you have to pay for the hardware and electricity. This concept of leader selection is therefore better than randomly selecting a node as a leader, since you can’t just increase the chance of being selected without paying a lot of money for it.
But what happens if by chance 2 miners solve the puzzle at the same time? That means they would both create a new block and publish it to the network. If both blocks are valid, the nodes have to decide which block to accept. In this case, each node accepts the block that they saw first. This means we may have 2 different states in our network, which is a problem we have to resolve. But there is a simple solution: We wait for the next block and see which of the 2 conflicting blocks this new block will be attached to. This will be the block that is accepted by the whole network, and every node that saw the wrong block first will have to discard that block and add the 2 new blocks to their copy of the Blockchain. So the rule is that the longest chain always wins (also called Nakamoto consensus). In the picture below B is the longest chain so the 2 blocks of A will be discarded.

This also means, that we shouldn’t accept every transaction the moment it’s added to the Blockchain, because it’s possible that the block containing this transaction will be dropped. So the larger the transactions, the more blocks you should wait to minimize the risk of your transaction being in a part of the Blockchain that gets dropped because another, longer Blockchain is found.
Proof of Stake
Proof of Stake is built on the assumption that users who have a lot of funds in the network don’t want to harm it because their funds would then be worth less. With Proof of Stake, users can use a node to stake some or all of their funds. These staked funds are locked and the chance that you get selected as leader is equal to the portion of your stake compared to the stake of the entire network. Just like in POW, if you are selected as leader, you get to decide which transactions will be included in the new block and other nodes will validate the block. POS seems like a much simpler concept and requires less energy compared to POW, but it gets tricky when it comes to the implementation details. Both systems have trade offs and lead to different behaviors of the network, which we will discuss later.
What are the incentives to provide resources to the network as a miner/staker?
To answer this question, the last component of a valid block becomes relevant: the block reward. When you create a new block, you are also allowed to create a predefined amount of new tokens and add them to any address you want. This block reward is the way block producer (i.e. miner/staker) earn money and also the reason why miners are called that way: They “mine” new tokens.
When you create a transaction, you can choose to pay a transaction fee to ensure the block producer includes your transaction in the block. If there are more new transactions than there is space in the block (demand > supply), most block producers only include the transactions with the highest transaction fees, as this increases their income. This can lead to exploding transaction fees in times of congestion. Popular Blockchains like Bitcoin and Ethereum are constantly in this congested state (more new transactions than block space). You can click here for a fun visualization of how many transactions are currently waiting to be processed in Bitcoin and Ethereum and here for a chart of their historical transaction fees.
With a way to select a leader that is allowed to create new blocks, our system is now able to ensure that all nodes update their Blockchain copies in the same way, i.e. reach consensus. In other words our system can :
☑ make sure that everyone in the network agrees on the ledger state (who has what balance), i.e. reach consensus
Since we have achieved all requirements that we stated in the beginning
☑ securely store all required data
☑ send and receive transactions
☑ make sure that all transactions are valid
☑ make sure that everyone in the network agrees on the ledger state (who has what balance), i.e. reach consensus
our proposed system is now usable as a currency.
However, until now we have assumed that the nodes and block producers act honestly. This is a very unrealistic assumption, so we need to make sure that nothing bad happens if there are some dishonest participants in the network. It is very hard (maybe impossible) to guarantee that there is no theoretical way to attack our network, but we can ensure that honest behavior is encouraged and dishonest behavior is punished. So our goal is to make sure that a fraudulent participant doesn’t get any advantage for being dishonest.
Since nodes and block producers are the only participants in the network, we’ll have a look at what happens when they act fraudulently.
Why should the block producer be honest and what happens if they are dishonest?
Miners/stakers are the block producers in our network. They can try to cheat (act in an unintended way) in multiple ways:
- add conflicting/invalid transaction to the block
- don’t add any transactions to the block
- give themselves a bigger block reward (create more new tokens than are allowed)
- try to double spend by secretly creating the longest chain
If the block producers add an invalid/conflicting transaction to the block or generate more tokens than are allowed, the nodes detect this when they check the new block for validity and simply reject it. This means that the block producer doesn’t receive his normal block reward and thus loses money because he wastes resources and receives no reward. In a POS system, you could punish the staker even more by taking away the staked tokens when the nodes detect fraudulent behavior.
Producing empty blocks without any transactions is another attack vector. If every block producer did this, the network would be useless as it would be impossible to send/receive transactions if they are never included in a block. This problem can be solved by adding transaction fees to your transaction. Transaction fees create inventives for honest behavior, because block producers that add your transactions to their block earn extra money. Therefore, it is very unlikely (but not impossible) that all block producers will ignore your transaction if you add a high enough transaction fee. If there are at least some honest block producers, the network will still be functional, albeit a bit slower.
Due to the longest chain wins rule, it would be possible that a malicious block producer tries to create the longest Blockchain without publishing the blocks to the network initially.

This would allow him to undo all transactions in the discarded blocks, including his own. In other words, he could spend his money again. To succeed, the malicious block producer would need more than 50% of the hash rate/staked funds of the entire network. In networks that already have a lot of hash rate/staked funds, it is very hard and expensive to get this much hash rate/staked funds, and therefore this attack is very unlikely if the resources are properly distributed.
What happens if the nodes are dishonest?
Nodes are responsible for storing and updating the Blockchain. A malicious node could try to attack the network by changing transactions that are already stored in the Blockchain. Other nodes would recognize this dishonest behavior because the hash of this block would also change if you modify a transaction. Therefore, all honest nodes would simply ignore the malicious node and keep their own (valid) copy of the Blockchain. This would create 2 versions of the Blockchain, the honest one and the attacker’s version. When there are 2 versions of a Blockchain, it is called a fork and each participant of the network can choose which nodes he wants to use and thus which version of the network to use. Since everyone can see that the malicious node has cheated, honest participants of the network will always chose the honest fork of the Blockchain and thus the network will be functional if there are at least some honest nodes.
This means, that the proposed system is not only able to
☑ securely store all required data
☑ send and receive transactions
☑ make sure that all transactions are valid
☑ make sure that everyone in the network agrees on the ledger state (who has what balance), i.e. reach consensus
but you also
☑ don’t have to trust any intermediaries
Therefore, Blockchains successfully solve the problem of processing, storing and sharing data in a trusted way without the need for intermediaries. Now that we understand how Blockchains works, let’s take a look at their properties:
Advantages of Blockchains compared to centralized solutions:
- The biggest and most important advantage of Blockchains is that there is no need to trust third parties or intermediaries.
- If the resources (hash rate or staked funds) are properly distributed and high enough that a new actor can’t easily get the majority, Blockchains are very secure.
- Currency-specific: You have a predefined monetary policy (inflation/deflation rates etc.) that is very unlikely (impossible if nodes don’t agree) to change later. This allows the users to join a network with their preferred policy and be sure that it won’t change suddenly.
Drawbacks of Blockchain compared to centralized solutions:
- Since Blockchains are a distributed network and every node has to store the same information. This is very inefficient compared to a central database.
- Due to the limited block size and the predefined time intervals for new blocks, Blockchains are not very scalable and rather expensive. Big blocks lead to node centralization because it’s expensive to run nodes. Too short time intervals between blocks also lead to node centralization, because you need a fast internet connection and a lot of computing power (to validate blocks) when new blocks are created very quickly. As we discussed earlier, centralization is bad because you have to trust the remaining nodes. And if you have to trust anyone, you have lost the main advantage of the Blockchain and are only left with its disadvantages.
There are a lot of second layer solutions that try to solve the scalability problem, but they introduce new trade offs (e.g. they are less secure than the Blockchain layer or centralized). - Blockchains have created a conflict of interests between block producers and users with the introduction of transaction fees. Block producers want high fees to generate more income, while users want low fees to save money. Block producers could try to increase the fees by not including low fee transactions in a block. They can also dictate the order of the transactions in a block, enabling them to create an order that is favorable to them and unfavorable for the user. This process is called Miner Extractable Value (MEV) if you want to read more about it.
- If the resources (hash rate, or staked funds) are poorly distributed, i.e. centralized, or too small, Blockchains are either not very secure or you have to rely on third parties, which would render the Blockchain useless.
- POW specific: Waste of resources. The mining process consumes a lot of energy to solve some useless puzzles to settle on a leader (block producer). The energy is not completely wasted as it’s used to secure the network, but if you can find another solution that is just as secure and doesn’t require as much energy, this solution would be much better.
- POS specific: Centralization risk due to block reward. In this system, the rich always get richer (if they stake their tokens) because they have a higher share of the staked tokens and therefore have a higher probability of winning the leader selection and receiving the block reward. They can stake the block reward again, which further increases their probability of winning the leader selection and receiving the block reward.
Blockchain conclusion
By using a Blockchain, you don’t have to trust intermediaries, but lose efficiency and low operation costs. This trade off may be worth it for some use cases where you really don’t want to trust a central party, but you should carefully consider what you need before choosing a Blockchain.
It is also noteworthy that many disadvantages (3. - 6.) stem from the leader selection. Disadvantage 2. results from the linear nature of transaction processing and the limited block size. Drawback 1. can’t be solved because storing data only once in a central database will always be more efficient (and insecure) than storing it in multiple distributed databases.
If we can find a way to process transactions asynchronously and add new transactions to our data structure without having to choose a leader to do so, we can solve pretty much all the drawbacks (2. - 6.) of Blockchains. This is exactly what the Tangle does.
What is IOTAs Tangle, and how does it solve the drawbacks of Blockchains?
We will talk about the decentralized version of IOTA and its features in the current testnet. At the time of writing this article, the mainnet is still running with a central coordinator (controlled by the IOTA Foundation) and is therefore not decentralized. However, the coordinators power is more limited than many think. The coordinator can NOT issue invalid transactions or manipulate transactions after their creation. The only thing it could do is not approve certain transactions and thus censor the network. Personally, I doubt IOTA Foundation would do such a thing, because of the loss of reputation. Nevertheless, the fact remains that they could do it as long as the coordinator exists. But since we’re going to talk about the decentralized version of IOTA, I don’t want to spent more time on talking about the coordinator.
TLDR:
The Tangle is a the underlying data structure of a cryptocurrency called IOTA. It uses the structure of a Directed Acyclic Graph (DAG) instead of a Blockchain in order to overcome the inefficiencies of current Blockchain designs and introduces a new way of reaching consensus. Each transaction is represented as a vertex in the graph. The vertices are connected with each other using a cryptographic hash function that ensures that the transactions cannot be modified. These connections between vertices are called edges. To issue a new transaction, you have to check 2–8 unconfirmed transactions (called tips) for their validity and can then append your new transaction to these transactions, adding 2–8 new edges to the DAG. This newly attached transaction is now a tip itself and can be validated by others who want to send a transaction. Since anyone is allowed to attach new transactions and thus update the DAG, this approach solves all the disadvantages of Blockchains that arise from the leader selection because there is no need to select a leader in the first place. Moreover, everyone is allowed to attach transactions at the same time. This asynchronous way of processing transactions leads to a much more scalable system. The resulting DAG is shared publicly so that anyone can participate in the network and verify the validity of the transactions.
What is the Tangle?
The Tangle is a the underlying data structure of a cryptocurrency called IOTA. It uses the structure of a Directed Acyclic Graph (DAG) instead of a Blockchain in order to overcome the inefficiencies of current Blockchain designs. A DAG is a graph consisting of vertices connected by edges. Edges are directed, i.e. you can only go in one direction. Acyclic means, that there are no closed loops in the graph if you follow the direction of the edges.
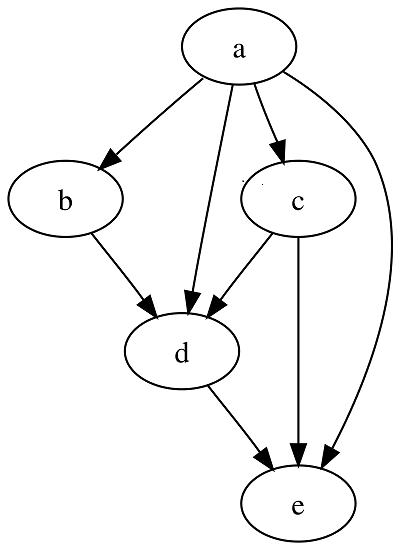
In the Tangle, each vertex of the graph consists of a single message. This message can either be a transaction in the form of “Alice pays Bob 20¢” or any other data. Similar to the section on Blockchains, we will only talk about transaction messages, so I’ll simply call them transactions for the rest of the article. The edges in the Tangle are hash pointers (more on them here if you skipped the Blockchain part), which ensures that the transactions cannot be modified. Each transaction is connected to 2–8 older transactions. The transactions you attach your new transaction to are called parents. The Tangle starts with a single initial transaction called genesis transaction. This genesis transaction created the entire token supply of IOTA (no new tokens are ever created) and is the only transaction that has no parents.
The image below shows how the Tangle looks like when each transaction is attached to 2 parents.

If you want to see a live visualization of the growing tangle, click here.
How do we send and receive money?
IOTA also uses a private and public key to send and receive money. If you skipped the Blockchain section, private and public keys are explained here. Just to reiterate: Always keep your private key (also called Seed) save and don’t share it with anyone! Without it, you lose access to your funds and if you share it, the person you shared it with gains access to your funds.
You need your private key to sign outgoing transactions and you use your public key as an address where others can send you money.
To issue a new transaction, you have to check 2–8 (preferably) unconfirmed transactions,called tips, for validity and then you can append your new transaction to these transactions, adding 2–8 new edges to the DAG. Additionally, you have to do a certain amount of Adaptive Proof of Work (APOW, explained in more detail later).
This newly attached transaction is now a tip itself and can be validated by others who want to send a transaction. In the Tangle, everyone is allowed to attach transactions at the same time (if they have enough access mana, more on this later). This asynchronous way of processing transaction leads to a very scalable system. Since everyone is allowed to attach transactions and thus update the Tangle, you don’t need any miners/stakers. The elimination of central block producers also means that you can get rid of transaction fees, because you don’t need them as an incentive for the block producers. The incentive to validate other transactions is that you need to do it to send your own transaction.
How do we make sure that all transactions are valid/honest?
In IOTA, all transactions in the Tangle get checked for their validity by all nodes that participate in the network.
A transaction is valid if:
- input amount = output amount
- input tokens aren’t already spent somewhere else
- issuer of transaction signed it using his private key
- contains at least 1 strong parent and 2–8 parents in sum
- contains nonce with correct difficulty
- contains timestamp that passes parent age checks
This list has introduced some new concepts we need to talk about. Lets start with the types of parents. A parent can either be strong or weak. Parents are marked as strong if you like all transactions in its past cone. The past cone of a transaction includes all transactions before it that are either directly or indirectly (through the parents of the transaction and their parents, etc.) connected to it. Similarly, the future cone of a transaction includes all transactions after it that are directly or indirectly connected to it. Parents are marked as weak if there are one or more transactions in it’s past cone that you dislike (i.e. consider invalid). The requirement of having at least one strong parent ensures that the transaction has a consistent history without any conflicts.
The image below shows an example of the Tangle with strong and weak parents. Note that not all parents of each transactions are shown. Transaction D is rejected by the protocol, but only after E and F have already referenced it. E and F are both valid, so they get picked up by G and H, but as weak parents, since G and H both dislike the past cone of E and F.

The reason why the concept of strong and weak parents were introduced will be explained later.
The parent age checks are:
- The timestamp of the parent is older than the timestamp of the transaction you want to attach.
- The timestamp of the parent is not older than some threshold value X.
The first check makes sure that the transactions are processed in the right order and the second check is needed to enable pruning (more on pruning later).
What is mana?
To understand how a lot of components of the IOTA protocol work, we have to first introduce a new concept called mana. Mana is the sybil protection mechanism of IOTA, i.e. it prevents an attacker from gaining undue influence over the network by creating multiple nodes (like POW and POS in Blockchains). When a value transaction is processed, mana is pledged to a node chosen by the token holder. The amount of the pledged mana is proportional to the amount of tokens transferred in the transaction. Mana and the tokens that generated the mana are connected. The mana of tokens can only be pledged to one node at a time.
Lets use an example to demonstrate this process: Suppose Alice sends a transaction to Bob and pledges the mana to node A. Now Bob uses the tokens he received from Alice and sends them to Charles. This means that the mana generated by the tokens is revoked from node A and pledged to an other node B (chosen by Bob).
Thus, the only way to obtain mana is to convince a token holder to pledge it to you or to buy the token yourself. Therefore, mana can be seen as Delegated Proof of Token Ownership. Since nodes require mana to influence consensus, it provides an adequate sybil protection because it is difficult to acquire in arbitrary quantities.
There are 2 types of mana, access mana and consensus mana. Nodes need access mana to be able to issue transactions. Consensus mana is used by the nodes for many different tasks, such as finding consensus, finding adequate neighbors for your node, and finalizing transactions. A transaction is considered final if enough new transactions reference it, directly or indirectly, so that the probability of dropping this transaction is very low. To decide if a transaction is final, a property called approval weight is measured. The approval weight of a transaction is proportional to the consensus mana in its future cone. That is, the more transactions (weighted by the issuing node’s consesus mana) that are in a transaction’s future cone, the more certain you can be that your transaction won’t be dropped.
To ensure maximal flexibility of the protocol, it’s allowed to pledge the access and consensus mana of a transaction to two different nodes.
How do we resolve conflicts?
Conflict handling in the Tangle is significantly more complex than in Blockchains. The reason for this is that Blockchains have a total order of transactions. Since blocks are added one after another and the block producer gets to dictate the order of transactions within a block, everybody agrees on which transaction was first. If you try to spend your money a second time in such a system, it is quite obvious for everyone in the network which transaction came first and thus is valid.
The Tangle doesn’t have a total order of transactions, so you have to find another way to handle conflicts. But let’s first understand why the Tangle doesn’t have this rather useful property. Nodes in a decentralized network are by definition spatially separated (distributed). Since multiple nodes are allowed to issue transactions at the same time and information can only travel at a maximum speed, nodes in different locations will naturally see the transactions in a different order. Thus, if a malicious actor issues two transactions with the same amount of money at the same time through two different nodes in different locations, the nodes of the network will have different opinions about which transaction came first. So when conflicts arise, the Tangle forks into different branches. This means that the IOTA protocol must be able to do 2 things:
- Decide which branches will get confirmed(only one of the conflicting branches can get confirmed)
- Record this decision for new nodes joining the network later
This is achieved through a voting mechanism called On Tangle Voting(OTV):
The nodes vote indirectly for a branch by attaching their transaction to it. Honest nodes will attach their transactions to the branch they see first or the branch with the most approval weight if they see multiple branches. If they notice that an other branch exists that has more approval weight than the branch they voted on, they attach a new transaction to this new branch and their approval weight gets subtracted from the previous branch. The approval weight of a branch is essentially the amount of consensus mana held by nodes which issued their last transaction on that branch. When the approval weight of a branch is more than 66% ahead of any conflicting branch, this branch is considered valid and the conflicting branches are considered as rejected. Nodes joining the network after the conflict know which branch is valid based on their approval weight.
Valid transactions that were attached to a rejected branch can be picked up into the master branch as weak parents, so you don’t have to issue those transactions again.
Let’s illustrate this process with an example: Alice has 5 MIOTA. First, she sends these 5 MIOTA to Bob via transaction A. Then Alice accidentally (or intentionally) sends these same 5 MIOTA to Charles in transaction B. Now we have two conflicting transactions, A and B, and the Tangle forks into three branches: branch 1 which includes A, branch 2 which includes B, and the master branch that includes all confirmed transactions.

When the nodes detect the conflict, they vote for the branch they like by attaching their transaction to it. In this example the protocol rejects branch 1 and confirms branch 2. This means that branch 2 will be merged into the master branch since there are no conflicts anymore.
Spam protection
Every DLT needs some form of spam protection, otherwise a malicious actor could flood the entire network with useless transactions and render it useless to honest participants. Blockchains have an implicit spam protection enforced by the mining difficulty and transaction fees.
The IOTA protocol doesn’t have any transaction fees and thus needs an explicit spam protection. IOTAs spam protection consists of a combination of access mana and Adaptive Proof of Work (APOW). To issue a new message, the issuing node required to compute a small Proof of Work. Similar to Blockchains, the POW consists of finding a nonce so that the hash of the transaction starts with a certain number of zeros determined by the difficulty. If the node tries to issue consecutive transactions in a short time interval, then it has to solve a progressively more difficult puzzle — making it impossible to create a burst of transactions. This mechanism acts as an emergency break during spam attacks by slowing down the rate of transactions a node can generate. The following graphic shows how the POW requirement is increased as the amount of transactions increases, and how the requirement drops when the amount of transactions drops:

To comprehend how small the POW requirement of IOTA is if you don’t spam the network, lets compare it to Bitcoin:
At the time of writing, Bitcoin has an estimated annual energy consumption of 80.5 TWh (according to the University of Cambridge). Assuming 7 TPS (Transactions per Second), this would result in
364kWh ≈ 1.3104 GJ (Gigajoule) for a single bitcoin transaction. To put this number into perspective: A single Bitcoin transaction consumes more energy than an average two-person household in Germany in an entire month (≈269 kWh, source). According to this Blogpost of the IF, the energy consumption of 1 IOTA transaction with easy POW is ≈4 J (Joule). This means we could send 327 million IOTA transactions with the energy consumed by a single Bitcoin transaction. This comparison is often criticized because Bitcoin doesn’t only use POW to issue transactions, but also to secure the network from attacks, which is a fair point. To make the comparison more realistic, I’ll try to calculate the additional energy consumption of the IOTA network. To do this, I need to make a few assumptions: Suppose the IOTA network consists of 1000 nodes running on a VPS, each consuming 10W, and the network load is 200 TPS. This leads to an additional energy consumption of 10*1000/200=50 J/Tx, i.e. the network would need an additional 50 J to validate a transaction. Thus, the energy consumption of the IOTA network to process and validate a transaction would be 54 J. This number would increase with the number of nodes and decrease with the TPS of the network. So the IOTA protocol would still require ≈24 million times less energy than Bitcoin to process a transaction and secure the network.
Access mana is used by IOTAs congestion control algorithm. Congestion occurs when the network has more traffic than it can handle. Without proper congestion control, the network can become oversaturated and cease to function because nodes can overwhelm their neighbors with more messages than can be handled by them. Therefore, the total throughput of the network (informally known as transactions per second) is ultimately limited by the available resources such as internet connectivity, device processing, and storage capacity. To prevent this oversaturation, the congestion control algorithm decides which transactions to forward based on the issuing node’s access mana. If a node issues more transactions than allowed by their access mana, its neighbors still won’t process them faster than the allowed rate. Thus, when you pledge access mana to a node, you are effectively pledging a portion of the network bandwidth to it. It’s important to note that this algorithm only comes into play if the network is congested. Currently there are about 20–50 TPS on IOTAs mainnet and it can handle 1000+ TPS, so this algorithm is probably not even needed in the immediate future.
The animation below shows how access mana affects a transactions ability to be issued into the tangle. Transactions issued by nodes with more access mana (the larger hexagons) enter the Tangle more frequently during times of congestion.

What happens if a node is malicious?
A malicious node can’t really harm the network unless it holds more than 50% of the consensus mana, which is very unlikely to ever happen. The adaptive POW and congestion control algorithm prevents oversaturation of the network and OTV makes sure that you can’t double spend if you hold less than 51% of the consensus mana. Since there are no mining/staking rewards in IOTA, it’s very unlikely that anyone will ever be able to accumulate that much consensus mana, as you would need 51% of all tokens (or enough user pledging their consensus mana to you) to do so.
What a malicious user could do is spamming the network to the point where the congestion control algorithm kicks in and then try to sell access mana to nodes that want to issue some transactions but don’t have enough access mana. For this attack, he would need a lot of access mana, because the more access mana a node has, the less the APOW increases for each transaction when you spam the network. The exact number of access mana you need to successfully perform this attack depends on protocol parameters (which I haven’t seen yet) and the general TPS of the network. It’s also important to keep in mind that even if this attack is successful, honest user can still issue transactions if they have access mana. If you have 10% of the total access mana, you are guaranteed to always have access to 10% of the network bandwidth.
How do we prevent node centralization?
The lack of incentives to run a node in the IOTA network is often criticized and I think that there’s a misunderstanding. The incentive to run a node in Blockchains and IOTA is exactly the same: being able to access and use the network. In Blockchains the block producers are rewarded with block rewards and transaction fees, not the node owners.
However, there is a valid concern that would lead to node centralization if not addressed: Since IOTA can process a lot of transactions very fast, the Tangle also grows very fast. All this data has to be stored somewhere. If a node had to keep all the transactions until the genesis transaction, it would take up a lot of storage space and become expensive over time. More expensive nodes always lead to centralization. But there is a solution to this problem called pruning.
Consider the following example: Let’s say you go to a bar and want to buy a drink for 5$ and you pay in cash. Neither you nor the barkeeper has to know who had these 5 $ before you. He can see that it’s a valid banknote and accepts it.
The same is true for a cryptocurrency. Since you can check the approval weight of each transaction, you know which transactions are valid. Therefore, you could drop every transaction that is already spent and only have to keep all unspent transactions (where “unspent” means, that you received this money and haven’t used it yet) in the Tangle. And this is basically what pruning does. You can set in the node software that you want to drop all spent transactions that are older than some threshold. This is also the reason why parents aren’t allowed to be older than a certain threshold, because it would make pruning very hard. As a node owner you can also decide to never prune anything and run a so called permanode, but this would get expensive over time. It is also possible to prove that a certain transaction was in the Tangle with a prove of inclusion, but that topic would require more explanation and I don’t want to make the article much longer than it already is.
Some critics say that if you don’t keep the full history until the genesis transaction, you could have an inflation bug without someone noticing it. I will talk about that in the “my personal opinion” section, because I try to keep my opinion out of the explanations.
Now we learned how IOTA is able to
☑ securely store all required data (Tangle)
☑ send and receive transactions
☑ make sure that all transactions are valid
☑ make sure that everyone in the network agrees on the ledger state (who has what balance), i.e. reach consensus
and you still
☑ don’t have to trust any intermediaries
So let’s take a look at IOTAs properties compared to Blockchains.
Advantages of IOTA over Blockchains:
- The IOTA version we talked about is truly decentralized. Everyone can issue their own transactions if they want. You don’t have to choose a single block producer each time a new block is created. Moreover, there is no mining reward that could lead to centralization in the future.
- IOTA is feeless. This means that the interests of all participants of the network are aligned, as there are no miners/stakers.
- IOTA is much more scalable than Blockchains. It can already process 1000+ TPS with very moderate node requirements and that number is likely to increase even before sharding (a scaling solution that enables virtually infinite TPS). Blockchains with similar TPS numbers are much more centralized and have much higher requirements to run a node. Blockchains just can’t scale if they want to keep their decentralization, IOTA can.
- IOTAs APOW is much more energy efficient than Blockchains running on POW (for a comparison to Bitcoin click here) and doesn’t have the centralization problem of POS systems.
Advantages of Blockchains over IOTA:
- Blockchains are more battle tested. The decentralized version of IOTA only runs in a testnet and needs to be thoroughly tested to ensure that it really works and that there are no attack vectors. Blockchains have proven over many years that they are secure if the resources are distributed properly.
- Blockchain is a much simpler technology. This means that it’s easier to understand and implement without introducing bugs.
Conclusion IOTA+Tangle
By using IOTA and the Tangle, you get the same benefits over central systems as Blockchains but without most of the drawbacks. The only disadvantages that remain are that due to the decentralized nature of the Tangle, it’s less efficient and scalable than a centralized solution. With sharding, IOTA could become virtually infinitely scalable in the future, but it will never be more efficient than a centralized solution.
Due to the fact that most nodes will most likely enable pruning, IOTA is more of a data and value transfer protocol than a decentralized database.
IF IOTA can make their system work without leaving any attack vectors, there are no advantages of Blockchains over IOTA left and therefore there would be no incentive to use a Blockchain instead of the Tangle. However, IOTA would have a lot of advantages over Blockchains and enable a lot of new use cases (maybe I will write some articles about them in the future).
Up to this point, I’ve tried to state only facts in this article and keep my personal opinion out of it as much as possible. If you find any errors please let me know in the comments. Those who are only interested in facts can skip this last section, as it’s only about my opinion and not about facts.
My PERSONAL OPINION
Disclaimer: I have invested some money in IOTA, so my opinion may be biased.
My thoughts on Blockchains:
Blockchain technology has a history of more than 10 years and proven to work within its limited use cases. But there are several obvious problems. The popular chains like Bitcoin and Ethereum are over their capacity limit and the transaction fees exploded without being even close to mass adoption. This just shows that they are not scalable. Other Blockchains are more scalable but centralized (like Binance Chain). Blockchains always have to make sacrifices in terms of scalability or decentralization, there is just no way around that. And yes, I’m aware that there are second layer solutions that try to solve the problems of the first layer. However, they always introduce new trade offs. They are often more scalable, but sacrifice decentralization and security.
I think the trajectory of most Blockchains and DLTs in general is toward more centralization rather than less. There are multiple reasons for this, scalability being one of them. Another reason is that some have realized that burning crazy amounts of energy in POW cannot be the solution and are switching over to POS. This means that the rich token holder can stake their token and are more likely to get the block reward, making them even richer in the process. If they keep on doing this, these projects will get more and more centralized over the years. In POW systems, it is more cost efficient to run big mining farms and therefore it’s likely that mining pools will be established. If there are only a few big mining pools securing the system, I wouldn’t call that very decentralized. And even if you are able to run a decentralized blockchain with POW, it requires so much energy to be secure that I don’t think it’s worth it in times of a climate crisis unless it’s 100% renewable energy. And even then I think there are better solutions.
IOTA is one of the few projects in the DLT space (that I know of) that has a trajectory towards more decentralization rather than less. But I have to admit that there is still some way to go before they achieve decentralization.
My thoughts on IOTA and the Tangle:
First I want to talk about some criticisms that I often hear about IOTA (or any other cryptocurrency except Bitcoin) and think that they’re unfounded:
- “All projects except for Bitcoin are centralized, because they are developed by a foundation or a small group of people.” I agree that the development of most cryptocurrencies is centralized. But that doesn’t make the network centralized. The distribution and number of nodes (and block producers) are an indication for how decentralized a currency is, as they validate the transactions. And they can just reject any updates. This doesn’t really happen yet, because most cryptocurrencies are still in their early development and not really functional yet, so it wouldn’t make any sense to reject updates. But once the network is functional, that may change. Bitcoin went through the same phase in it’s early days and is still considered decentralized. The other cryptocurrencies are just earlier in their journey, but that doesn’t mean that they won’t get there. I even think it’s beneficial to have a centralized development until you have a functional network that achieved its vision, because central development is much faster. And after the first functional version, the nodes can decide whether they like new updates or not.
- “If you prune transactions, there could be an unnoticed inflation bug in IOTA.” Since you check for every transaction that the input amount is equal to the output amount and there is no mining that creates new tokens, I think this bug is impossible. But even if we consider that it would be possible, I think pruning is no problem because if you don’t detect the bug very fast, you can’t do anything about it anyway. To better understand what I mean, let’s consider the following example: We detect an inflation bug in Bitcoin that happened 6 months ago. There is nothing you can do about it. You can’t just roll back 6 months of transactions because all merchants that accepted Bitcoin in this time period would lose their money. And if you would only roll back the transaction where the inflation happened, the reputation loss would most likely still kill the project.
- “IOTA isn’t really feeless, because you have to do a small amount of POW to issue a transaction and that’s a fee!” This just doesn’t make any sense to me at all. If you pay something with your cellphone, your cellphone has to be turned on and also consumes energy, but we don’t consider this as a transaction fee. If you send someone 100 iota from your wallet, he gets exactly 100 iota, so there’s no transaction fee. Yes, someone has to run a node and yes this node consumes energy, but let’s consider you go to your favorite bar and the barkeeper accepts iota as payment. He runs an IOTA node in order to be able to issue transactions and when you pay your drinks, you use his node to send your transactions. Yes, his node has to do some POW and yes he has to pay for the electricity, but you as customer don’t have to pay any fee, i.e. there are no transaction fees. Now you might ask yourself why he would allow you to issue a transaction over his node for free. Well the answer is simple: The costs are so small that the benefit of having access to a valuable network far outweighs them. The opportunity cost of running hardware is not a transaction fee.
In the early days of IOTA, there was much hype about the project and very little technology to show for it. At the time, the IOTA Foundation also promised a lot of things and kept very few of them, so I can understand if you lost your trust in them and the project. To be completely honest, I have no idea why I didn’t lose my trust after all the things that happened, but I’m happy about it because the trajectory they are on right now looks very promising. They got rid of some problematic people, hype less and have a way better technology now. If there’s one thing I’ve achieved with my article, it’s hopefully that I’ve piqued your interest in the technology and you’ll look at it with an open mind. If you still don’t like it after that, that’s fine.
IOTA is much more complex than your average Blockchain, but I think to achieve their vision it’s worth going the extra mile. You should keep in mind that the Tangle and a lot of other concepts in IOTA are new and not very battle tested yet. So if security is your primary concern, you need a decentralized solution and this solution doesn’t have to be very scalable, I would probably go for a Blockchain right now. But I think over time this will change when IOTA has had the chance to prove itself. And yes, there is a possibility that IOTA will fail, but if we only did things that we were sure would work, there would never be any progress.
The main advantage I see for IOTA is, that unlike Blockchains, it doesn’t have any theoretical limits (aside from physical limits). If the developers make the right design choices, IOTA can enable almost limitless use cases. There is also a lot of exciting stuff in development right now that I haven’t talked about in this article, like Colored Coins, NFTs, Smart Contracts, etc. (Maybe also a topic for future blog posts?) I really think that if they get it right, IOTA has a bright future ahead. And I think the odds of getting it right are very good. But like I said, the tech is quite complex and the implementation details matter a lot, so don’t take my word for it, because anything can happen.
General thoughts about the DLT space:
Currently, all consensus mechanism (POW, POS, OTV, etc.) are weighted directly or indirectly by the amount of money you have. This means that if you’re rich, your opinion matters more. I think it would be great to find a solution where this is not the case. In the real world, more money doesn’t make you more trustworthy. I trust the people I know well because they have built up a reputation with me. If we can find a way to incorporate this real world trust into a DLT, that would be the best consensus mechanism I can think of.
What I don’t like about the DLT space right now is the cult-like and irrational behavior of many people in it. Just because you put some money into a project doesn’t mean it has the better tech and all other projects are shit. There are a lot of maximalists in this space that talk down everything another project does and praise even the flaws of their preferred project. I don’t know if that’s the sunken cost fallacy talking, but I really don’t like it. I know this might sound funny coming from me after an article like this, but I hope I was able to explain why I actually think IOTA has the better tech. If you find some errors in my reasoning or know a better technology, please let me know in the comments!
The DLT space shouldn’t be viewed as a get rich quick scheme, but as an enabler of a wide variety of previously impossible use cases. It gives many people access to a global monetary system for the first time. The fact that your money possibly gains value over time could help eliminate the throwaway society. DLTs can make supply chains more transparent and let customers make informed decisions, like only buying products that are ethically produced. They can help you reclaim ownership of your data and monetize it yourself, if you choose to do so. Feeless transactions enable micro transactions and pay-per-use applications. The tech could help to facilitate a green revolution and combat the climate crisis (and no, I don’t think Bitcoins POW in it’s current form can be a part of that). And so much more. DLTs can change the world for the better and that’s their true value, not some account balances that are going up fast. Most people in the cryptocurrency space are only looking at the money side of things. They don’t even look at the vision and tech of a project and what benefits it could bring to the world. I would really like to see that change, and if this article can bring us a little closer to that, I’ll have achieved my goal.
Kudos if you actually made it through this whole thing. I hope it was worth your time, and if it sparked your interest in DLTs, have fun down the rabbit hole.
If you want to learn more about IOTA, make sure to join the official Discord or check out the Wiki.
